I’m a bit confused on the wordage here. It says Active Directory is “a database of network objects” which is hosted on a Domain Controller which “provides authentication services to users”.
To walk through it, if I’m a user connecting to a fileserver on a network, I would connect to the Domain Controller, say “hey DC I’m so-and-so here’s proof connect me to fileserver pls ty” and then it would check the AD for the address and connect provided I’m authorized to do so. Is the check for whether I’m authorized to connect done by the DC with its own config or is it something in the AD that says “if so-and-so tries to connect let them in”?
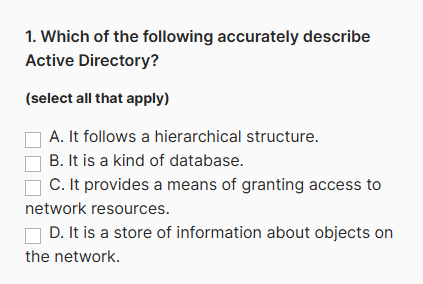
The first question is a true/false stating “Active Directory provides a means of granting access to network resources”. My gut response was false as in my head I’m basically equating AD to a file system which is just the idea of links and hierarchy and the DC is like the OS that accesses it. Like, say you wanted to have it so certain network objects were hidden to most users. The DC would be checking users first and then providing a list of what that user can see or access, right? So isn’t it entirely the DC granting access then? I guess one could say AD “provides a means of granting access to network resources” since the DC needs a list to work off of.
Actually after rereading this a couple times, I think I figured it out, but any input would still be appreciated just to make sure I’m understanding it right.