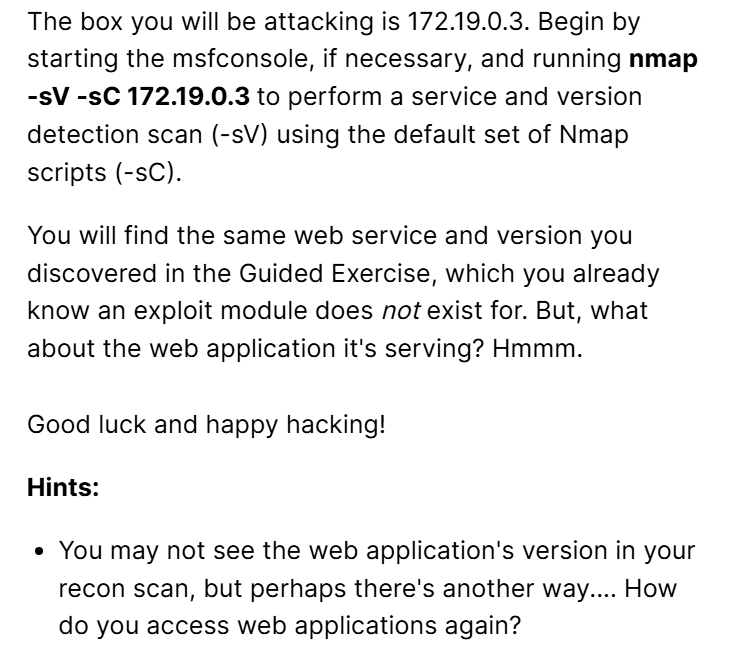
Hi, I’m currently stuck on this challenge and I don’t understand what I’m supposed to get from the web service, can someone please advice.
This challenge is very similar to the lab:
1.) Close and restart Metasploit, best to start clean
2.) In Metasploit, run an nmap scan as instructed to discover a web server and a web service
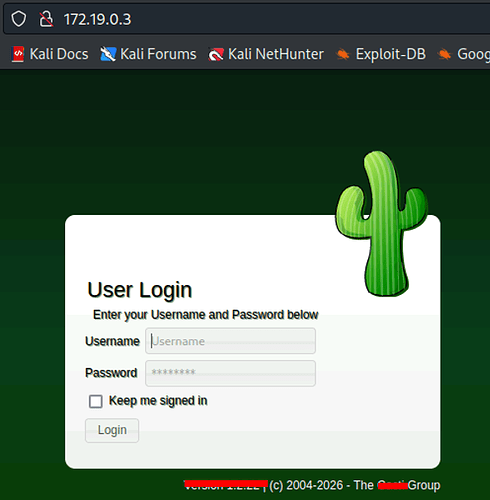
Our focus is on the web service. Nmap will not tell us the version, but there is a huge hint on finding it using some other tool (not Metasploit). How do we visit a website? (Hint, you are using one right now to do this lab.)
4.) In Metasploit, search for the web service found and use an exploit matching the version. This will give you a meterpreter shell (no need to upgrade)
6.) Leverage the meterpreter session to suggest a local exploit like you did in the guided exercises.
7.) Use and run the suggested exploit
8.) Search for the flag, and cat the flag.
1st question: just simply run the command <firefox 172.19.0.3:80>
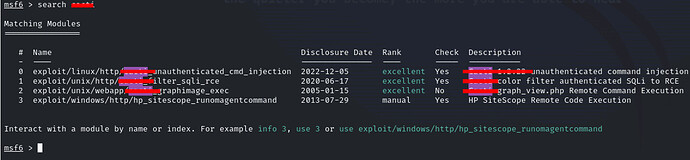
2nd question: run the command <search <that particular module name from question 1> >
3rd question: Use that module and do all the settings as told , run once , then follow the guided exercise part 2 number 9 to the end
1st question: That or just open Firefox and visit 172.19.0.3 ![]()
2nd question:
3rd question: Use that module and do all the settings as told , run once , then follow the guided exercise part 2 number 9 to the end
Looks right ![]()
Thank you for the help, was very useful. I got confused and instead of looking for the actual web service I was looking into the one we didn’t have a version available and from there I went down the spiral. I struggled a bit getting a session but found out where I missed. Thanks again for your help. I completed the challenge ![]()